ACME & FreeIPA – super easy
This post will be short. Recent FreeIPA versions contain ACME server implementation, which makes TLS certificate issuance a breeze.
- FreeIPA
-
FreeIPA is a solution giving you LDAP for user accounts, CA for issuing certificates and Kerberos for SSO, delivered with nice WebUI in an integrated package.
- ACME
-
Automated Certificate Management Environment is a protocol designed to automate process of getting a TLS certificate. It was popularised by Let's Encrypt, BuyPass, Venafi and others.
When you have FreeIPA, you have your own Certificate Authority. It is most sensible to use it for securing your internal endpoints. Your clients should already trust this CA. Your internal network may not be reachable by external ACME providers. And you may want to hide your internal hostnames from appearing in global Certificate Transparency Databases.
Ready to start? Make sure package pki-acme is installed on you FreeIPA server. Next, enable ACME functionality:
$ ipa-acme-manage enable
The ipa-acme-manage command was successful
Done! Now configure the client – for my k8s I'm using awesome cert-manager. Start with definition of a ClusterIssuer with your FreeIPA URL (put you own email and server address, of course):
--- kind: ClusterIssuer apiVersion: cert-manager.io/v1 metadata: name: pipebreaker-freeipa spec: acme: email: tomek@pipebreaker.pl server: https://ipa-ca.pipebreaker.pl/acme/directory privateKeySecretRef: # Secret resource that will be used to store the account's private key. name: issuer-pbrk-account-key solvers: - http01: ingress: {}
Second (and last) step is to annotate each ingress which should get a TLS certificate automatically provided:
--- kind: Ingress apiVersion: networking.k8s.io/v1 metadata: annotations: cert-manager.io/cluster-issuer: pipebreaker-freeipa […]
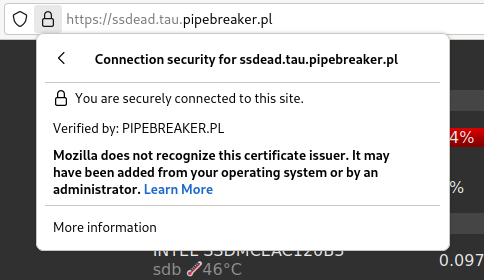
And that's basically it. After few moments certificate should be issued:
When using cert-manager, make sure it's version 1.6.0 or later. There was a fix for ambiguity in spec which solved some interoperability problems with FreeIPA implementation. The fix may be backported for older cert-manager releases.
 Tomasz Torcz
Tomasz Torcz
Comments
Comments powered by Disqus